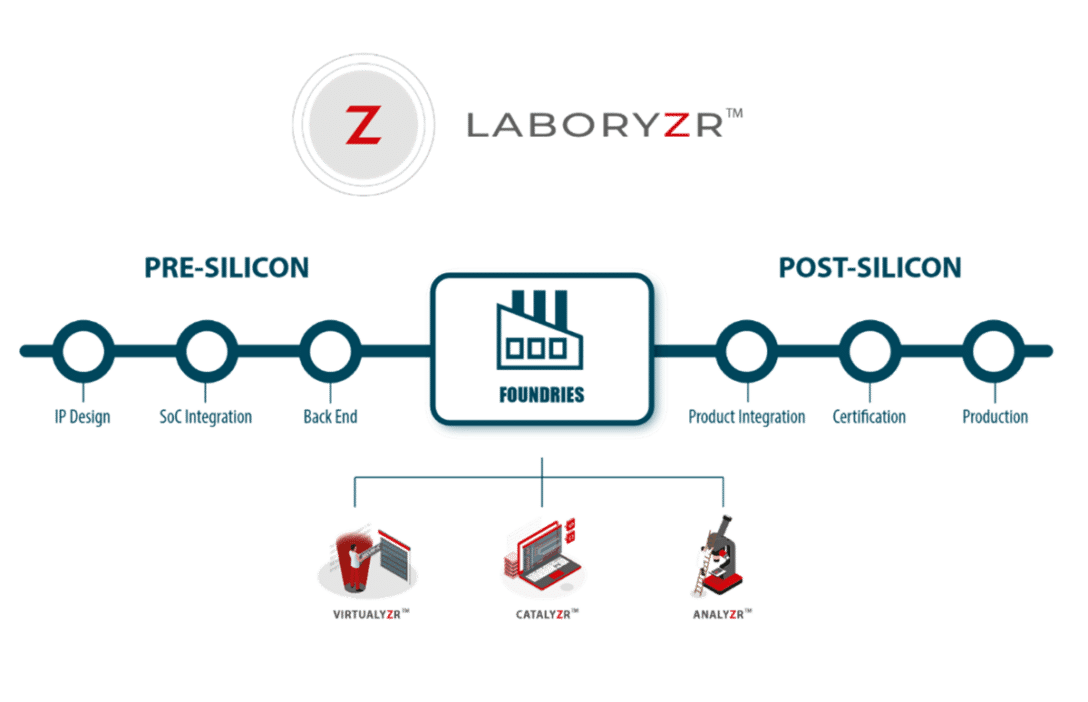
Laboryzr™
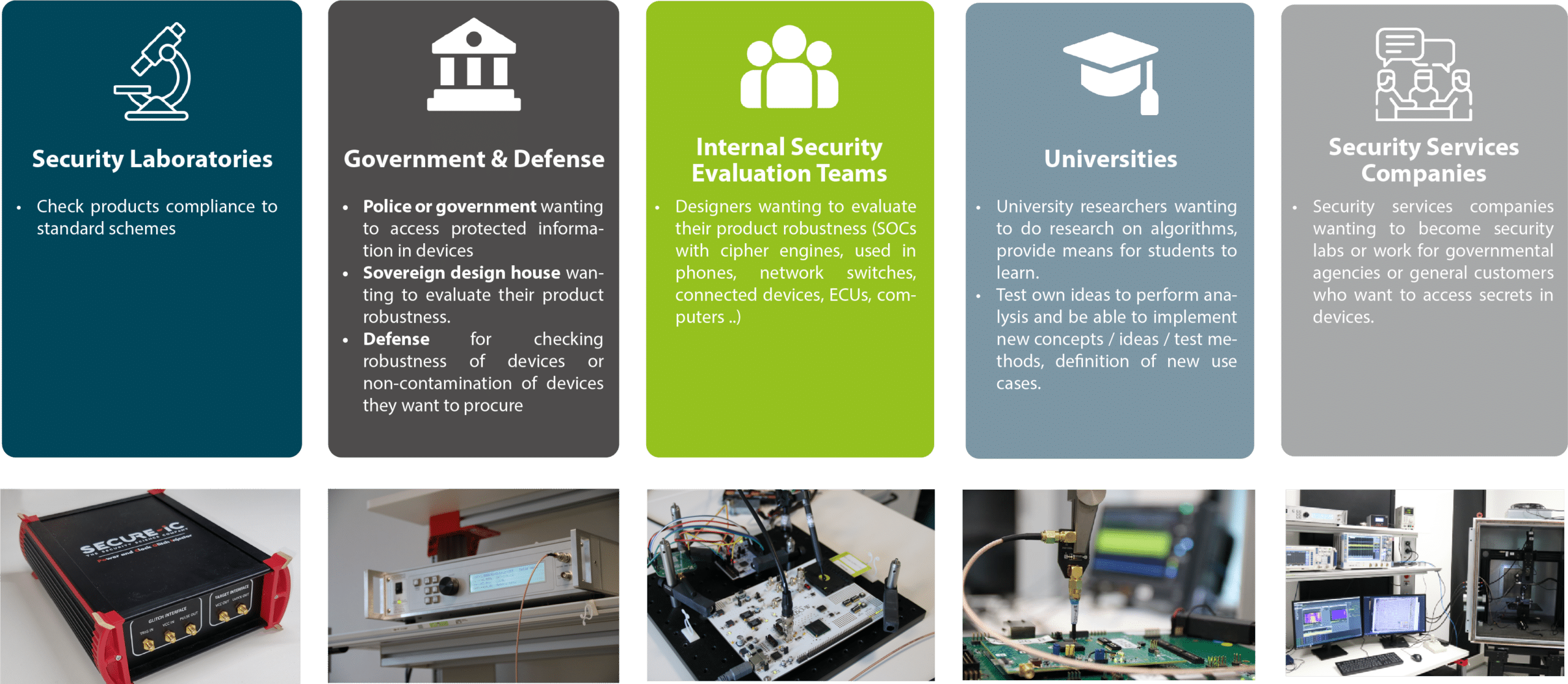
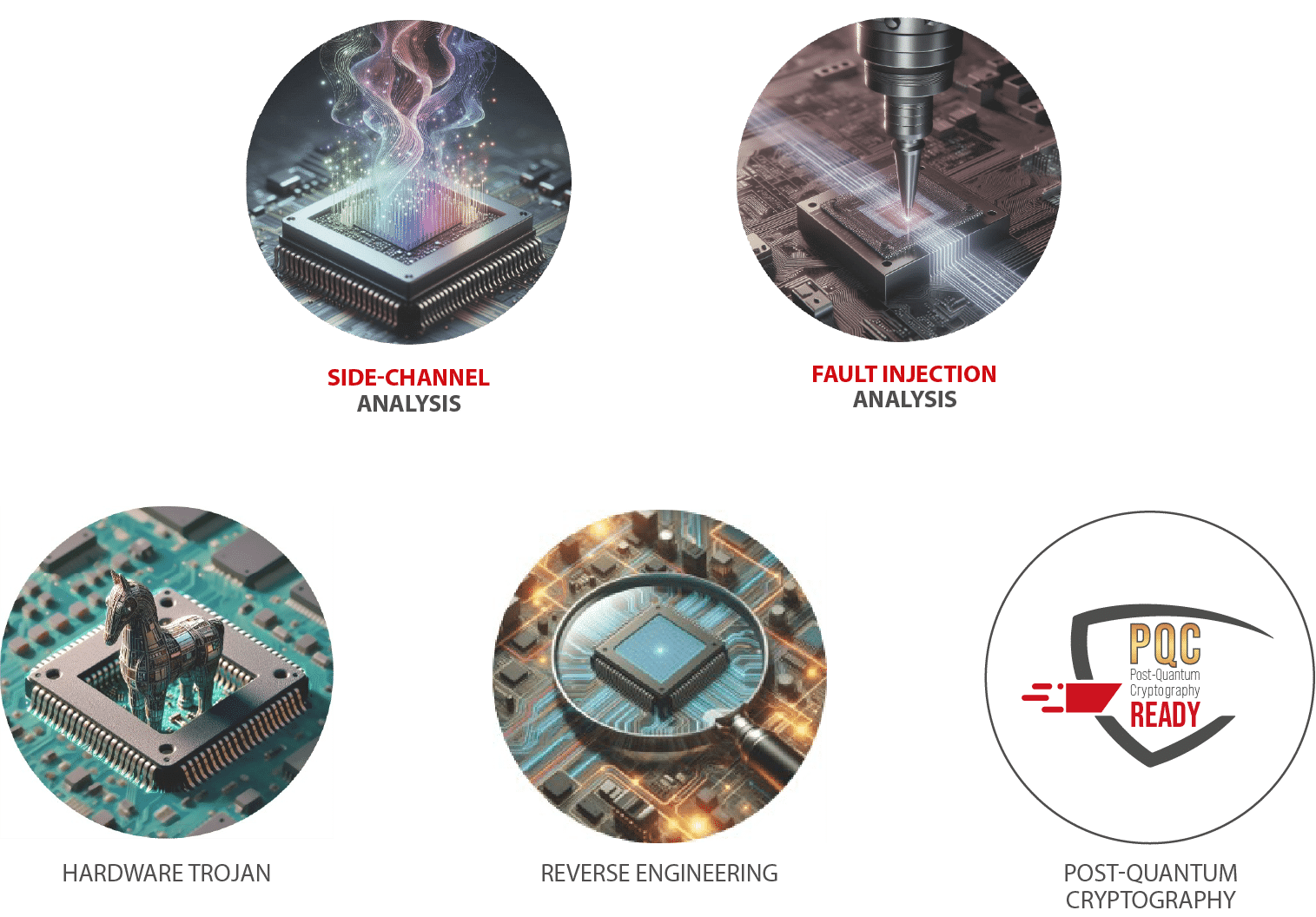
How to ensure that your devices are secure against cyber-attacks and do not present any potential vulnerabilities? Security evaluations allow to determine clearly the degree of compliance of your devices to a specific security model or a targeted security standard.
With Laboryzr™ solution, Secure-IC offers to evaluate your full design process, from pre-silicon, to post-silicon and security risk assessment.
It had never been easier to ensure security along the product life cycle!

From Pre-Silicon to Post-Silicon
- Pre-silicon validation:
- allows for early detection and resolution of issues through hardware simulations before the manufacturing stage.
- Post-silicon validation:
- focuses on physical testing after the silicon chip is fabricated (ASIC, FPGA, IoT, Smartphone, Smartcard, Microcontroller…)
- Software assessment:
- is as important as assessing the hardware to ensure the level of security.
Fully Compliant with Certification Standards
Secure-IC supports its customers reach their desired certification levels with general certifications such as Common Criteria, FIPS-140, ISO, SESIP; but also, to reach their target in more specific standards such as CC AVA_VAN up to level 5, ISO/IEC 17825, OSCCA…
Laboryzr™ includes
- Transfer of technical know-how
- Training for full autonomy
- Long term support to keep an updated expertise
- State-of-the-art solution updates