Virtualyzr™ Pre-Silicon Verification (HW)
Virtualyzr™ facilitate your security evaluation with specifically Hardware Design verification tools.
Pre-silicon evaluation is a key step on the SoC design flow since it helps reduce time-to-market as well as post tape-out maintenance. By finely emulating the behavior of a device at the design stage, it is possible to anticipate and protect against security weaknesses before the foundry.
Pre-Silicon evaluation with VirtualyzrTM
Fully Compliant with Certification Standards
Secure-IC supports its customers reach their desired certification levels with general certifications such as Common Criteria, FIPS-140, ISO, SESIP ; but also to reach their target in more specific standards such as CC AVA_VAN up to level 5, ISO/IEC 17825, OSCCA..
VIRTUALYZR™ Workflow
Simulation
The design is simulated through EDA Tools and according to its conception level “top and down” (RTL / Post Synthesis / Place & Route) and stimuli configuration. Simulated results are obtained, commonly VCD output, and the user can select the part of its design to be evaluated with Virtualyzr™.
Traces generation
Selecting the part of its design to be evaluated, simulated results (or external VCD database) are investigated and processed based on a mathematical consumption model.
Analysis & Report
An advanced physical analysis is performed on the obtained leakage traces. Two types of analysis can then be performed: side-channel analysis and fault injection attacks analysis up to complete evaluation report.
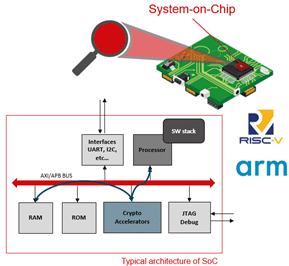
VIRTUALYZR™ for System on Chip
Security Evaluation must concern SoC where security is vulnerable such as Crypto accelerators and Critical parts of SW code on CPU.
Virtualyzr™ allows evaluation of mixed design: Hardware and Software.
Virtualyzr™ can perform evaluation on RISC-V processor widely used in modern technologies (IoT, FPGA, etc.) and ARM-V2 basic processor of ARM architecture widely used in most of new technologies (smartphones, etc.
Combined Infrastructure
Graphical User Interface for Analysis Build & Test
- User-friendly interaction
- Allows unitary testing
- User has access to ready-to-use Use Cases or build his own including homemade development
- Easy to integrate to your regression test system
Command Line Interface for Full Automation
- Full scripting-based
- Allows automatic and chaining testing for end-to-end evaluation
- Suitable to feat EDA functional verification
- Easy to integrate to your regression test system
Advanced Expertise & Transfer Knowledge
- SCA & FIA Market Methodologies: SmartPhone, IoT, Microcontroller, Automotive, FPGA, SmartCard, Side Channel Analysis for Reverse Engineering…
More information about Expertyzr™